| Zero trust is now a top priority for most organizations, but new research from CyberRisk Alliance Business Intelligence, the research and content arm of cybersecurity data and insights company CyberRisk Alliance (CRA), shows efforts to deploy the framework facing headwinds – specifically over concerns about the user experience and impact on the business. Of the 200+ security and IT leaders and executives, practitioners, and compliance professionals surveyed, nearly 25 percent of those who have partially or fully implemented zero trust say they struggle to get full buy-in from other departments when it comes to scaling these ideas across the enterprise due to configuration issues (e.g., legacy apps that don’t interact well with zero-trust technology).As one respondent put it, “completely transforming the technology infrastructure takes time. Even if an organization has a sound architecture model and support from the business, executing is what matters — and those that don’t execute accordingly will never meet the intentions of zero trust in the first place.”
Another respondent said, “Zero trust addresses the modern challenges of today’s business, including securing remote workers, hybrid cloud environments, and ransomware threats.” But according to another respondent, “It’s difficult to find human resources with zero-trust skills, and we don’t have supporting infrastructure and appropriate identity and access management (IAM) tools to enforce the zero-trust framework.” Despite its perceived importance, “getting upper management to completely sign off on the need for zero trust is also a challenge.” Key takeaways:Only 24% of respondents have partially or fully implemented zero trust. Respondents say they continue to struggle with understanding the principals and configuration of zero trust. Nearly two-thirds of future zero trust adopters expect to have moderate difficulty in implementing it. Another 30% expect high difficulty. Pain points: ensuring it meets business needs, plays well with legacy apps and doesn’t disrupt user experience. Of those who are more advanced in their zero-trust implementation, 69% are motivated by pressure to close data security holes. MFA, IAM and least privilege access are the most common components of zero-trust strategies and implementations. Only one-third have formal zero trust policies. Zero trust marks a monumental shift in philosophy/practice. Respondents describe it as a “dramatic paradigm shift in security philosophy” that will require strategically reassessing how to secure the entire infrastructure to address challenges of remote or hybrid offices, multi-cloud environments, identity and authentication, and rapidly expanding endpoints. In addition to survey insights, the report offers guidance to inspire organizations to pursue zero trust with greater awareness around implementation. For more detailed findings and analysis, the full research report is available for download here. |
| CyberRisk Alliance (CRA) is a business intelligence company serving the high growth, rapidly evolving cybersecurity community with a diversified portfolio of services that inform, educate, build community, and inspire an efficient marketplace. Our trusted information leverages a unique network of journalists, analysts and influencers, policymakers, and practitioners. CRA’s brands include SC Media, Security Weekly, ChannelE2E, MSSP Alert, InfoSec World, Identiverse, Cybersecurity Collaboration Forum, its research unit CRA Business Intelligence, the peer-to-peer CISO membership network, Cybersecurity Collaborative, and now, the Official Cyber Security Summit and TECHEXPO Top Secret. Click here to learn more.
|
Author Profile

-
Dr. Perumal Koshy is associated with the Enterprise Futures Lab and is a columnist focused on institutional governance and economic systems. He writes on MSMEs, enterprise development, and policy issues affecting small business ecosystems.
Linkedin: https://www.linkedin.com/in/caushie/
Latest entries
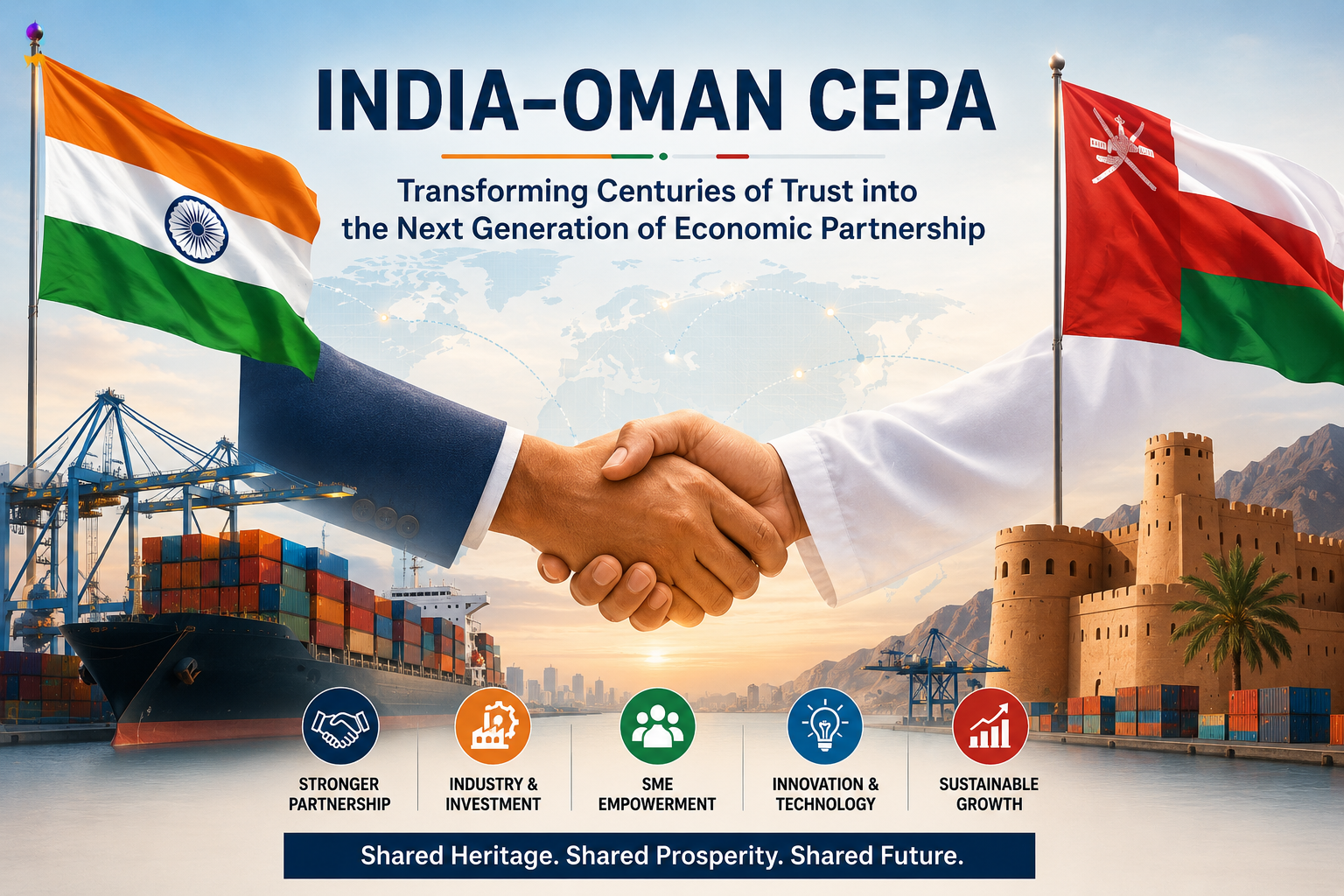
 Business2 June 2026India–Oman CEPA: Transforming Centuries of Trust into the Next Generation of Economic Partnership
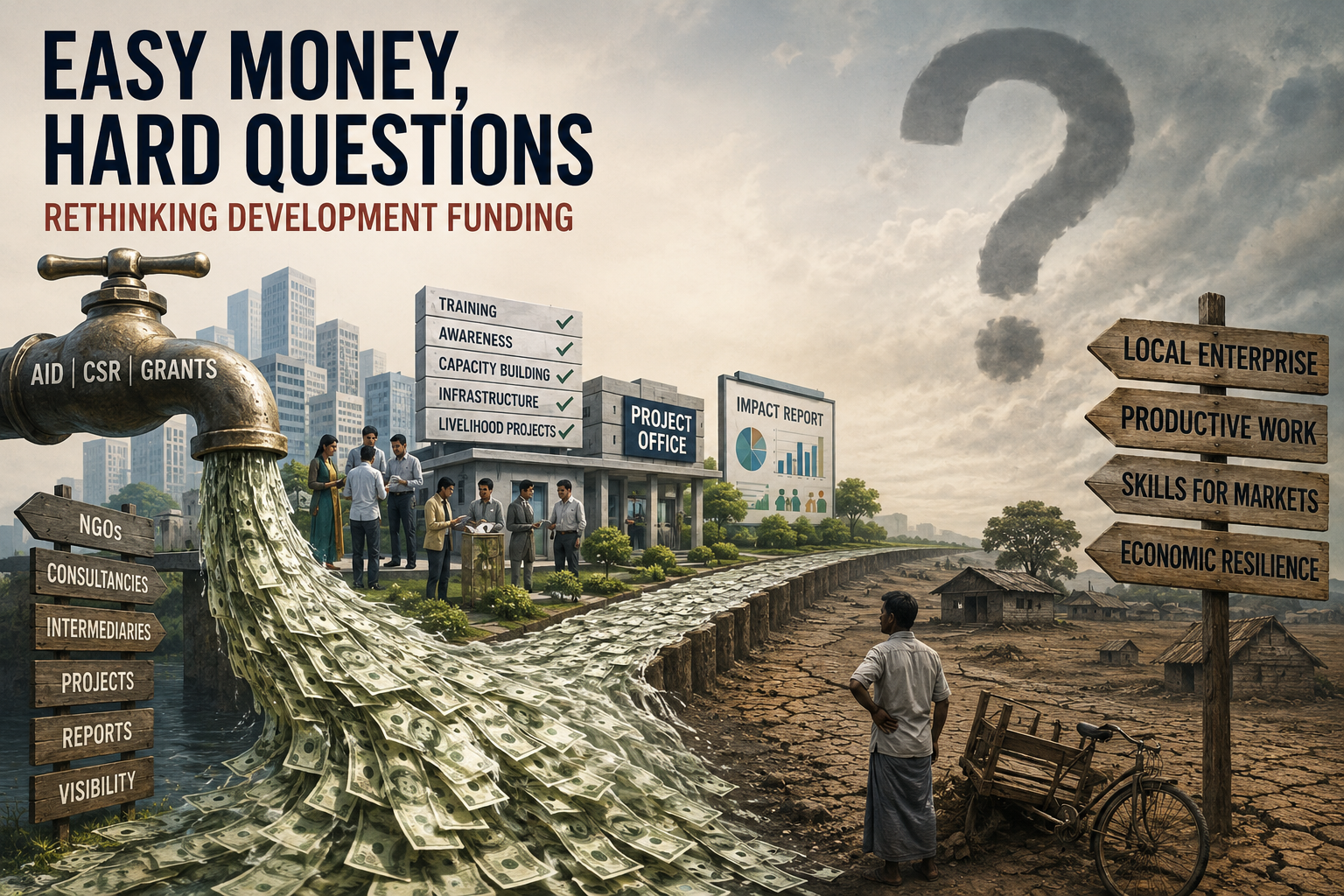
Business2 June 2026India–Oman CEPA: Transforming Centuries of Trust into the Next Generation of Economic Partnership Africa20 May 2026Easy Money, Hard Questions: Rethinking Development Funding
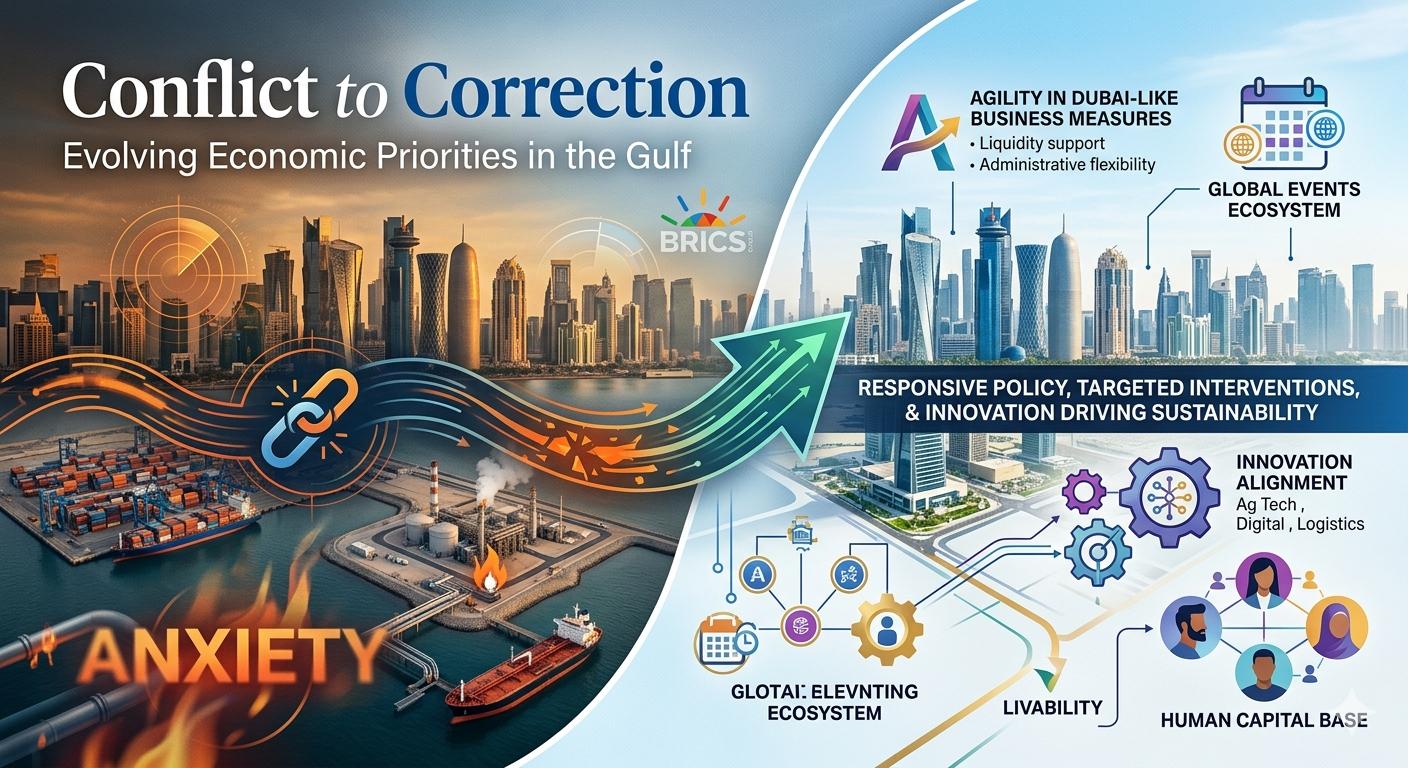
Africa20 May 2026Easy Money, Hard Questions: Rethinking Development Funding FEATURED10 April 2026From Conflict to Correction: Evolving Economic Priorities in the Gulf
FEATURED10 April 2026From Conflict to Correction: Evolving Economic Priorities in the Gulf FEATURED2 February 2026Outlook 2026 | Real Estate: Infrastructure-Led Growth, Integrated Communities, and the Trust Imperative
FEATURED2 February 2026Outlook 2026 | Real Estate: Infrastructure-Led Growth, Integrated Communities, and the Trust Imperative